CVEs What Are CVEs and Why Are They Important
Learning objective: By the end of this lesson, students will be able to define Common Vulnerabilities and Exposures (CVEs) and explain their role in identifying security risks.
What are Common Vulnerabilities and Exposures (CVEs)?
CVEs are a catalog of thousands of publicly disclosed cybersecurity vulnerabilities maintained by MITRE Corporation.
The CVE catalog provides a standardized reference for discussing vulnerabilities. The catalog makes it easier for organizations to identify and address security risks systematically, ensuring their systems remain secure and resilient against potential threats.
You can access the catalog online at cve.org.
To get a brief example of a CVE, search the CVE list for CVE-2021-34527: This is a known Windows Print Spooler vulnerability (commonly known as PrintNightmare) that allows attackers to execute malicious code on an affected system.
Why CVEs matter
CVEs act as a universal language for identifying vulnerabilities. By providing a standardized framework, CVEs ensure that organizations, researchers, and security vendors can communicate clearly and efficiently about specific security flaws, leaving no room for ambiguity.
CVEs are more than just identifiers; they are critical tools for effective risk management. They help organizations systematically evaluate vulnerabilities within their systems, prioritize the ones that pose the most significant threat, and take proactive steps to mitigate potential damage.
Without CVEs, tracking and addressing vulnerabilities would be chaotic, exposing organizations to an ever-expanding array of cyber threats.
The role of CVEs in addressing risks
CVEs play a crucial role in the process of identifying security risks and working to mitigate them; here’s a brief outline of how security professionals use them:
- Standardization: CVEs offer a standardized reference for discussing and addressing vulnerabilities, ensuring consistency across different platforms and organizations.
- Risk assessment: Each CVE entry includes detailed information and often a CVSS (Common Vulnerability Scoring System) score that measures severity.
- Prioritization: CVEs enable organizations to prioritize their efforts by focusing on the most critical, actively exploited vulnerabilities first.
- Collaboration: CVEs facilitate collaboration among security professionals, researchers, and vendors by providing a common language and framework for discussing vulnerabilities.
- Awareness and education: CVEs raise awareness about potential security risks and allow security professionals to more easily educate their organizations on the importance of timely updates and patches.
- Proactive defense: By staying informed about CVEs, organizations can implement proactive measures to defend against known vulnerabilities, reducing the risk of exploitation.
A compromised server scenario
Imagine a server at your company is suddenly compromised. The IT team realized it was because of an unpatched vulnerability. This situation could have been prevented by doing the following:
- Understanding and utilizing the Common Vulnerabilities and Exposures (CVE) system to discuss and prioritize risks effectively.
- Proactively identify and address vulnerabilities before bad actors can exploit them.
- Conduct regular security audits to identify and address vulnerabilities before they can be exploited.
- Ensure that all employees are trained on cybersecurity best practices and the importance of timely software updates.
- Utilize automated tools to scan for vulnerabilities and apply patches promptly.
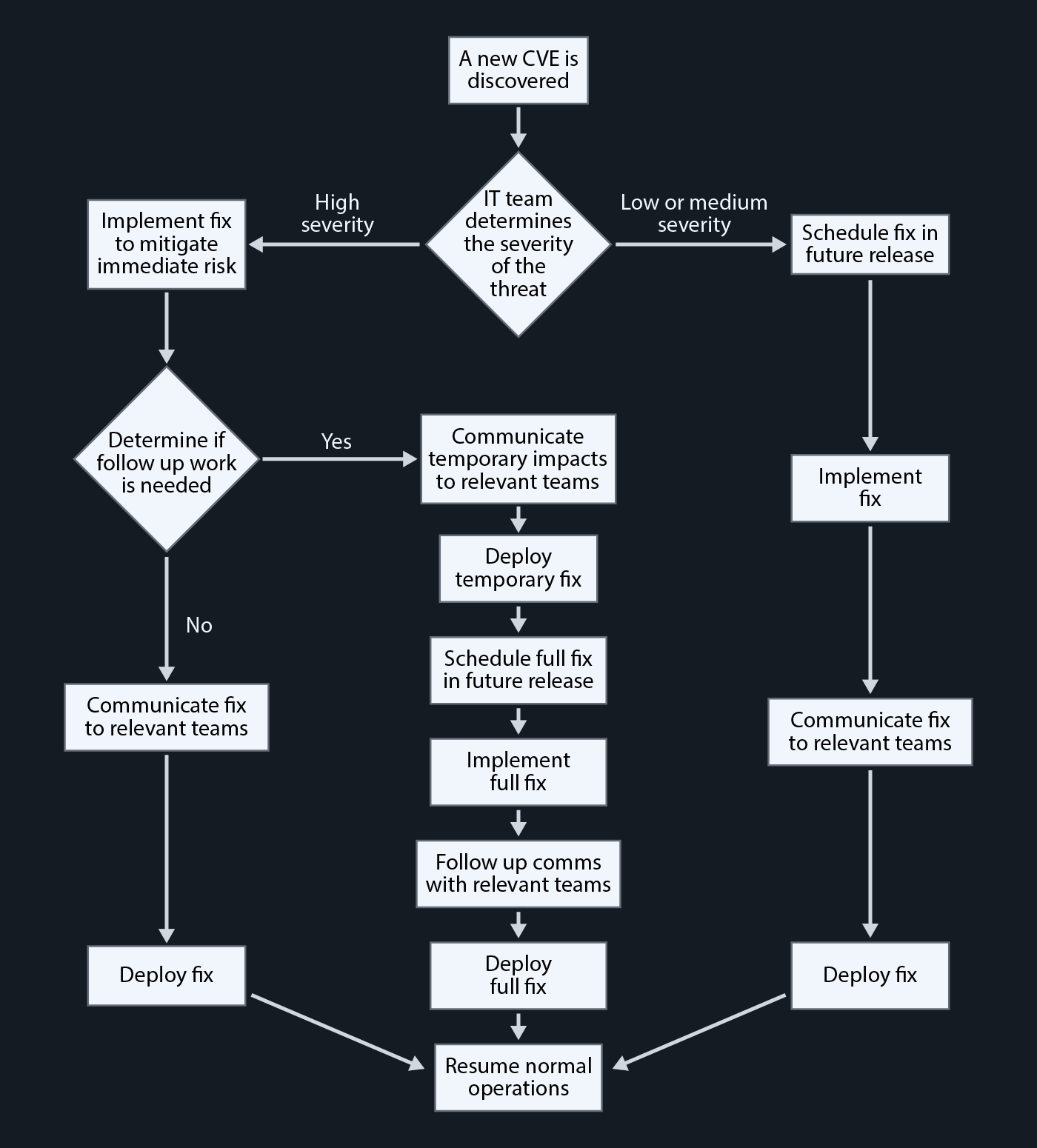
Workflow
Below is a diagram of an example workflow for how organizations utilize the CVE system to identify and address vulnerabilities: